Description
Fortinet FortiAnalyzer 1000E Kuwaitcity
Fortinet FortiAnalyzer 1000E provides deep insights into advanced threats through Single-Pane Orchestration, Automation & Response for your entire attack surface to reduce risks and improve your organization’s overall security. Integrated with Fortinet’s Security Fabric, FortiAnalyzer simplifies the complexity of analyzing and monitoring new and emerging technologies that have expanded the attack surface, and delivers end-to-end visibility, helping you identify and eliminate threats. Advanced Threat Detection & Correlation allows Security & Network teams to immediately identify and respond to network security threats across the infrastructure.
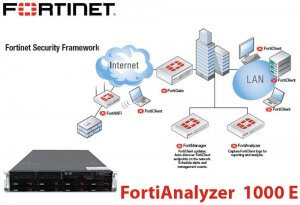
Fortianalyzer 1000e Kuwait 1
In Fortinet FortiAnalyzer 1000E Automated Workflows & Compliance Reporting provides customizable dashboards, reports and advanced workflow handlers for both Security & Network teams to accelerate workflows & assist with regulation and compliance audits. Scalable Log Management collects logs from FortiGate, FortiClient, FortiManager, FortiSandbox, FortiMail, FortiWeb, FortiAuthenticator, Generic syslog and others. Deploy as an individual unit or optimized for a specific operation and scale storage based on retention requirements.
FortiAnalyzer 1000E Features :
-
End-to-end visibility
Event correlation, threat detection and Indicator of Compromise (IOC) service reduce time-to-detect and identity threats
-
Fortinet Security Fabric integration
Correlates with logs from FortiClient, FortiSandbox, FortiWeb, and FortiMail for deeper visibility and critical network insights
-
Enterprise-grade high availability
Automatically back-up FortiAnalyzer DB’s (up to 4 node cluster) that can be geographically dispersed for disaster recovery
-
Security automation
Reduce complexity and leverage automation via REST API, scripts, connectors, and automation stitches to expedite security response
-
Multi-tenancy and administrative domains (ADOMs)
Separate customer data and manage domains leveraging ADOMs to be compliant and operationally effective
-
Flexible deployment options & archival storage
Supports deployment of appliance, VM, hosted or cloud. Use AWS, Azure or Google to archive logs as a secondary storage
-
Security Operations Center (SOC)
FortiAnalyzer’s SOC management center helps secure your overall network by providing actionable views of log and threat data. Protect your network, web sites, applications, databases, servers and data centers, and other technologies, with centralized monitoring, awareness of the threats, events and network activity, using predefined and customized dashboards delivered through a single-pane-of-glass interface for easy integration into your Security Fabric.
-
Incident Detection & Response
FortiAnalyzer’s Automated Incident Response capability improves Management & Analytics with a focus on event management and identification of compromised endpoints. Improved default and custom event handlers can be used to detect malicious and suspicious activities on the spot. Integration of events with the FOS automation framework for automated actions such as endpoint quarantine or blacklist IPs. Incident detection and tracking, as well as evidence collection and analysis, are streamlined through integration with ITSM platforms, helping to bridge gaps in your Security Operations Center and reinforce your Security Posture.
Event handlers enable quick detection, automated correlation and connected remediation with incident management to simplify log analysis and threat identification across your Fortinet Security Fabric. Create event handlers for FortiGate, FortiCarrier, FortiCache, FortiMail, FortiManager, FortiWeb, FortiSandbox devices, and syslog servers. Define what messages to extract from logs and display in events and send alerts for event handlers via email address, webhook, SNMP community, or syslog server.
-
Indicators of Compromise
The Indicators of Compromise (IOC) summary shows end users with suspicious web usage compromises. It provides information such as end users’ IP addresses, hostname, group, OS, overall threat rating, a Map View, and a number of threats that you can drill down to view the details. Analysts can re-scan historical logs for threat hunting, and identify threats based on new intelligence. To generate the Indicators of Compromise, FortiAnalyzer checks web filter, DNS and traffic logs of each end-user against its threat database. When a threat match is found, a threat score is given to the end-user. FortiAnalyzer aggregates the threat scores of an end-user and gives its verdict of the end user’s overall Indicators of Compromise. The Indicators of Compromise summary is produced through logs from the FortiGate devices and FortiAnalyzer subscription to FortiGuard to keep its local threat database synced with the FortiGuard threat database.
-
Reports
FortiAnalyzer provides 39 built-in templates that are ready to use, with sample reports to help identify the right report for you. You can generate custom data reports from logs by using the Reports feature. Run reports on-demand or on a schedule with automated email notifications, uploads and an easy to manage calendar view. Create custom reports with the 300 built-in charts and datasets ready for creating your custom reports, with flexible report formats include PDF, HTML, CSV, and XML.
-
Log Forwarding for Third-Party Integration
You can forward logs from a FortiAnalyzer unit to another FortiAnalyzer unit, a syslog server, or a Common Event Format (CEF) server. The client is the FortiAnalyzer unit that forwards logs to another device. The server is the FortiAnalyzer unit, syslog server, or CEF server that receives the logs. In addition to forwarding logs to another unit or server, the client retains a local copy of the logs. The local copy of the logs is subject to the data policy settings for archived logs. Logs are forwarded in real-time or near real-time as they are received. Forwarded content files include: DLP files, antivirus quarantine files, and IPS packet captures.
-
Analyzer-Collector Mode
You can deploy in Analyzer mode and Collector mode on different FortiAnalyzer units and make the units work together to improve the overall performance of log receiving, analysis, and reporting. When FortiAnalyzer is in Collector mode, its primary task is forwarding logs of the connected devices to an Analyzer and archiving the logs. The Analyzer offloads the log-receiving task to the Collector so that the Analyzer can focus on data analysis and report generation. This maximizes the Collector’s log receiving performance.
-
Multi-Tenancy with Flexible Quota Management
Time-based archive/analytic log data policy per Administrative Domain (ADOM), automated quota management based on the defined policy, and trending graphs to guide policy configuration and usage monitoring.